Worried about having your credit card hacked? How about if a criminal, a hacker or even a government agency could turn your gun on or off anytime they wanted? While so-called “smart guns” aren’t yet ready for prime time, the tools to hack one variety of them already exist; they just haven’t been applied to a product not yet actually on the market.
There are currently three main paths to “personalizing” firearms or so-called “smart guns”: fingerprint reader, biometric and Radio Frequency IDentification (RFID). RFID is used on products ranging from active wear at major retailers, to military shipping containers to car keys.
RFID can be active or passive, with the former requiring a power source, i.e., a battery. Think of a security badge around your neck as passive example and the device in your car that lifts the bar and allows you to go through a toll booth as an active example. Passive RFID chips have no power source of their own and start broadcasting data when in range of an emitter, typically very close.
Most RFID chips are not encrypted-some are even left writable-but encrypted RFID chips are made, although they cost more. Presumably so-called “smart gun” makers would be smart enough to provide encrypted RFID chips, but even those can be blocked or hacked. A dedicated or “brute-force” attack, according to some security experts, can hack just about any RFID tag in a relatively short period of time.
The firm getting the most attention for its so-called “smart gun” RFID technology is the German company Armatix GmbH. The company also does electronic locks intended for police agencies and station houses. According to its website, issue arms can be locked up and set on a timer that only allows them to be removed from a cradle when a specific signal is sent to an RFID chip. It can tell you when it was accessed and by whom. And it can remotely either lock or release all the guns so stored. Armatix also makes a nifty, extremely complex “mechatronic” chamber insert that blocks the chamber of a firearm.
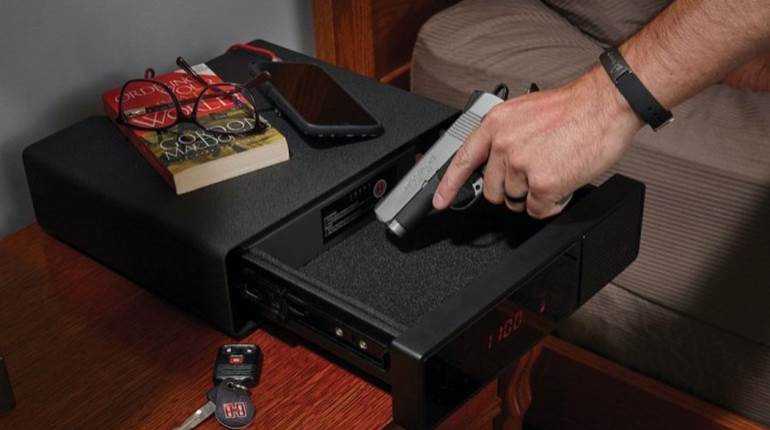
But the product generating headlines is the prototype of Armatix’s blowback-operated .22 Long Rifle iP1 pistol and its accompanying iW1 active RFID watch. The watch has an RFID emitter the company claims must be within “an operating distance of up to 15 inches,” meaning if the gun is not in the hand wearing the watch, the gun is deactivated. So much for weak-handed shooting. And before the pistol can be “enabled” the user must first enter a PIN on the watch, which is said to have “extensive watch functions.”
Typically, an RFID signal requires proximity, and blocking or reducing its range can be as easy as wrapping either the passive or active elements in tinfoil. Even more interesting to me was watching a short web commercial for an active RFID jammer that prevents information from being transmitted from a credit card to a hacker’s receiver. Could such active countermeasures be used to prevent an armed citizen’s firearm from being enabled? Not being a hacker or having access to an RFID-equipped firearm, I don’t know. But it is a question worth asking.
Police officers, just like defensively-minded armed citizens, need to know that their firearms, especially their defensive handguns, are reliable 100 percent of the time. In a March 19, 2014, article, United Press International’s Christopher Haubursin described serious concerns police have about using such guns, Haubursin wrote: “Hacking poses a particularly big threat in high-pressure situations, [National Association of Police Organizations Executive Director Bill] Johnson said. If police electronic gun security information is stolen like Target’s customer credit card information was this year, he said, the results could be devastating.” It continued with, “It’s part of human nature,” Johnson said. “As soon as this technology comes in, there’ll be someone trying to defeat it.”
What is the future of such technology? How effective and reliable will it be? How easy will it be to hack? We simply do not know. The problem, though, comes when misguided politicians, who don’t know an ejection port from a USB port mandate the use of technology they don’t understand. Three states passed laws mandating the future use of so-called “smart guns” before a fully functioning prototype existed-let alone was tested by objective third parties. They may as well have mandated the use of a “Star Wars” laser blaster for all their understanding of how they actually will work.
Check out this video for a better visual of RFID.